
When threat response operates without business context, it defaults to reactive mode. Every threat report becomes urgent because there’s no baseline for what matters most to the business. Organizations catalog threats, estimate likelihoods, and call it risk management, but if they never started with business priorities, they don’t have the context to decide which threats actually warrant attention. What gets called a “risk register” is often really a threat register with risk calculations bolted on. The risk context was never really about risk in the first place.
What most “risk registers” actually look like

The threat register as illustrated above shows security work, but it doesn’t answer the critical question: what actually breaks if these threats succeed? Without that, you’re just making lists.
What a risk register should look like
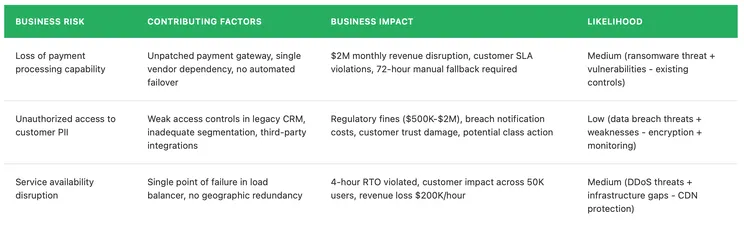
With the business context in this register, you can make informed treatment decisions. Loss of payment processing capability gets escalated for mitigation ($2M revenue exposure warrants investment in automated failover). PII access stays under monitoring since likelihood is already low, with documented accepted risk. Service availability gets mitigated with geographic redundancy and improved load balancing. Each decision ties back to business impact, not just threat severity.
Strategic and tactical threat assessment
The risk register establishes what matters to your business. Threat assessment identifies active and emerging threats. The connection between them determines whether threat response is reactive scrambling or strategic action.
Threat work happens at two different levels. Strategic threat assessment analyzes the macro landscape to inform defense priorities. Tactical threat response evaluates specific emerging threats to determine immediate action. Both depend on risk context. Without it, strategic analysis becomes academic threat cataloging and tactical response turns into emergency mode for every alert.
Risk context provides the framework for deciding what matters at both levels.
Strategic threat landscape analysis
Strategic threat assessment analyzes the broader landscape affecting your organization. You’re reviewing ransomware trends targeting similar organizations, nation-state activity in your sector, and MITRE ATT&CK techniques that apply to your environment. Some teams do this quarterly, others less frequently, but the goal is prioritizing defense investments based on real threats.
Risk context transforms this strategic work into defense priorities. When you review ransomware trends targeting financial services, you’re not just cataloging the threat. You already know from your risk register that payment processing capability is a $2M monthly revenue exposure with specific SLA commitments. That context tells you where to focus ransomware defenses, payment gateway resilience, vendor dependencies, automated failover, not just generic backup strategies.
Without that business context, landscape analysis turns into academic threat cataloging where everything looks equally important.
Tactical threat response
Then there’s tactical threat response when something specific emerges. A zero-day drops, your threat intel feed lights up with activity in your sector, someone forwards you a report about a new campaign. Your vendor sends an alert about active exploitation of a vulnerability in products you’re running. You need to assess exposure quickly and decide what to do about it.
Say threat intelligence comes in about a campaign targeting payment processing systems in your industry. Sophisticated attackers, specific techniques, actively operating. If you’ve done the risk assessment work, you already know whether payment processing is critical to your business. You know which systems support it, who owns them, and what kind of downtime the business can tolerate. You can check exposure against what you know and communicate to leadership in terms they understand, the same terms they used when they helped you identify those priorities in the first place.
Threats rarely map to a single risk cleanly. That same campaign targeting payment systems might impact revenue if transactions stop processing, regulatory standing if cardholder data is compromised, and customer trust if the incident becomes public. Risk context helps you understand which of those potential impacts matter most to your organization and respond accordingly. You might tolerate some downtime but can’t accept regulatory exposure. Or reputational damage could be the primary concern. The threat is the same, but the response priorities depend on what the business cares about.
Without that foundation, you burn time determining scope and impact instead of making informed decisions about defensive action. This isn’t hypothetical. We saw this play out with MOVEit, Accellion, and Citrix vulnerabilities. Organizations spent days building asset inventories, identifying which vendors had exposure, and piecing together what data was at risk while adversaries were already extracting it. Teams that already understood their critical data flows and third-party dependencies could respond within hours instead of days.
Putting this into practice
This works best when it’s built into how your team operates. Annual risk assessment establishes what matters through business engagement. Periodic threat landscape reviews keep you current on who’s targeting organizations like yours. Targeted threat assessments happen as threats emerge, connecting new intelligence to existing risk context.
Better threat intelligence doesn’t transform reactive scrambling into strategic response. Risk context does. It tells you what matters before the threat shows up.